Best Suggestions On Selecting Credit Card Apps
Wiki Article
How Do I Determine The Status Of My Card As Being Stolen In The Us?
Follow these steps: 1. Contact your credit card issuer.
For customer service, dial the number on the back of your credit card.
You may ask the representative to verify the status of the card.
It is possible that you will be required to reveal information regarding your identity as well as a credit card for verification.
Check Your Account Online
Log into the account of your credit card, or online banking which matches the card.
You can look for notifications, alerts and other messages about the status of your card.
Check the recent transactions and identify suspicious or unauthorized activity.
Monitor Your Credit Report
Obtain a free copy of your credit report from each of the three major credit bureaus (Equifax, Experian, TransUnion) through AnnualCreditReport.com.
Examine the credit report to see if there are any credit inquiries or accounts which you do not recognize. This could indicate fraud.
Security Alerts and Fraud Alerts Freeze
You may want to consider placing an alert about fraud or a security freeze on your credit report if suspect identity theft or fraud.
A fraud alert informs creditors to take extra steps to confirm your identity before extending credit, whereas a security freeze limits access to your credit report.
Watch out for any suspicious behavior and immediately report any suspicious activity.
Check your credit card statements regularly and immediately notify any suspicious or unauthorised transaction.
If you suspect fraud, or incidents of identity theft to the local law enforcement agency, as well as the Federal Trade Commission.
By contacting the credit card company, looking over account activity online, checking credit reports and remaining alert for indications of illegal activity, you can be proactive in protecting yourself from any issues that may result from a report of fraud on your credit card.
What Does It Mean For My Credit Card To Be On A Blacklist?
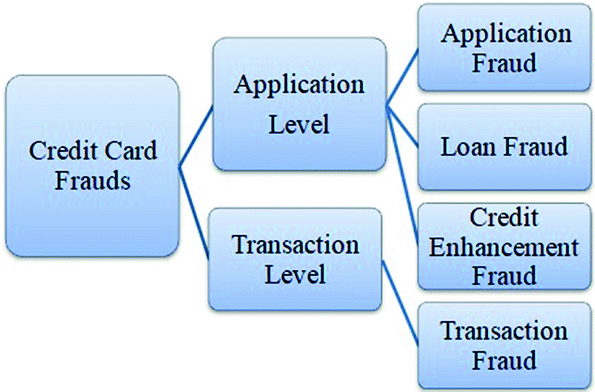
If a debit or credit card is put on a"blacklist," it is a sign that certain transactions are temporarily prohibited until the issue is addressed or confirmed. The reasons that a card may be placed on a blacklist vary and could include.
Suspected Fraud- Unusual or suspicious transactions made on the card that are detected as fraud could lead to the card being restricted for security reasons.
Security concerns. If evidence suggests possible security breach, such as unauthorized access, or data breaches which involves card information or unusual spending patterns then the card is flagged.
Identity Verification Issues- Challenges in proving the identity of the cardholder when making transactions, particularly in cases where additional verification is needed, could cause the card to be temporarily blocked.
Card stolen or lost If a credit card has been reported stolen or lost the issuer could place a block to prevent misuse of the card until replacement is issued.
Suspicious activity indicators- Any actions or behavior associated with the card, that could raise suspicions (such as several declined transactions or geographical anomalies), or any unusual spending pattern, could result in a temporary suspension.
A card that is listed on the blacklist could limit the ability of the holder to apply for credit or purchase items using the card. This could happen until the issuer has confirmed the legitimacy of the account or addresses any security or fraud concerns. It's crucial for the owner of the card to get in touch with the issuer immediately to resolve the issue, verify the validity of transactions, and deal with any potential security concerns related to the card.
How Can Cybersecurity Experts Detect And Monitor Cyber-Attacks Which Include Stolen Credit Card Data?
Security professionals monitor and detect threats such as compromised credit card numbers by using various techniques and tools. A few of these techniques and methods include: Threat Intelligence Gathering
Gathering information from various sources, including forums, threat intelligence feeds dark web monitoring and security advisory to stay informed about the latest security threats and security vulnerabilities.
Network Monitoring & Intrusion Detection
Monitor network traffic using specialized tools or software. Find out if there are any suspicious patterns that could signal unauthorized access or breaches of data.
Assessments of vulnerability and penetration testing
Regular tests can help you identify weak points in applications, networks, and systems. Penetration testing is a simulation attack that exposes weaknesses and evaluates the security posture of an organisation.
Security Information and Event Management Systems (SIEMs)
Implementing SIEM solutions to aggregate and analyze logs from a variety of sources, like firewalls and servers, to detect and react to security incidents instantly.
Behavioral Analytics -
Conducting behavior analysis to spot abnormal patterns or changes in normal user behavior in networks and systems that may be a sign of a security breach.
Threat Hunting
By studying logs and information from systems, you can identify threats to your company's network.
Endpoint Security Solutions
Installing endpoint security tools (such as anti-malware, antivirus, and endpoint detection tools and responses) to shield individual devices and endpoints from harmful activities.
Encryption of Data and Data Protection
Use encryption to safeguard sensitive information, like credit card information both in transit and while at rest.
Incident Response & Forensics
Develop and implement plans for incident response in order to respond swiftly to security incidents. Conducting forensic analysis to investigate and comprehend the nature of, the impact, and the source of security breach.
Cybersecurity experts integrate these strategies with a thorough understanding of evolving cyber-security threats, compliance requirements, and best methods to identify ways to mitigate and respond to cyber threats, such as those that involve compromised credit card data. Cyber threats can be defended through a combination of constant surveillance, information about threats, as well as proactive security. See the best savastan0 review for more examples.